Samir Saran| Sean Kanuck
Technology and transformation
In many parts of the world, tensions offline are now mirrored online. In the manner of a Wachowskis movie, machines influence both realities and the perception of such realities, often expressed online. The challenge for those seeking to “govern” or “regulate” cyberspace, then, is the umbilical connection between digital networks and their offline effects. How do you cut the cord? One or another way of regulating cyberspace today may have unintended consequences for all facets of economic life, social engagements and political discourse. Many governments, acknowledging this problem, have tried to regulate the effects of technology, rather than the technologies themselves. This year’s edition of Digital Debates explores, in twelve engaging pieces, how this process of “cyber-“ regulation has been influenced by watershed political and military events, upending the role of state and non-state actors as traditionally understood.
The year 2017 was tumultuous for politics, economics, and international relations. While the global community was still coming to terms with the United Kingdom’s decision to exit the European Union, the American public voted for Donald Trump, who may be described as the unlikeliest yet of candidates to have contested the US presidency. President Trump ran a campaign that many had considered antithetical to the soul of America—the free flow of capital and people. By most indications, Trump is determined to reshape American foreign policy, global governance institutions, international trade and security.
President Trump’s ascent to the White House — and indeed, the manner in which this was made possible — gives the international community an opportunity to reflect on the questions that are confronting cyberspace. Three developments are noteworthy, foremost of which was the shadow cast by Russia on the US presidential campaign. In an operation previously unheard of in American shores, Russia hacked into the Democratic National Committee’s database and selectively leaked information that would eventually damage contender Hilary Clinton’s efforts and favour Donald Trump. With this act, Russia showed the world how influence operations and information warfare can disrupt even the most entrenched democratic processes. It also signalled the brazenness of new technologies; nothing is sacrosanct.
Elina Noor, in ‘Reconsidering cyber security’ and Sean Kanuck, in ‘Hacking democracy’write about Russia’s influence campaign in 2016 aimed at the US presidential elections, noting how attacks in the future will continue to affect integrity of information infrastructures.
The second issue deserving of attention was Hilary Clinton’s reliance on Artificial Intelligence (AI) and Big Data to make decisions during her campaign. For instance, confident in her team’s analytical model which predicted that it was not necessary to spend time on the ground in Michigan and Wisconsin, Clinton failed to address what might have been a key constituency. Analysts say this oversight contributed to her loss.
A third focal point was the role of social media: in his campaign, Trump relied heavily on Twitter and Facebook to reach out to his audience, effectively bypassing the traditional media of print and television. Importantly, through algorithmic tailoring and personalised news feeds, social media was also responsible for creating what is called “information echo chambers” and polarising voters in the process.
Since assuming office, Donald Trump has worked to influence the US’ digital policies and the government’s role in cyberspace. Trump’s withdrawal from the Trans-Pacific Partnership (TPP), which would have represented approximately 40 percent of global GDP and 25 percent of world exports, has imperiled the US’ influence over digital norms. These norms would arguably have improved e-commerce and standardised internet rights amongst its member states. Similarly, Trump’s nationalist leanings have created uncertainty over America’s immigration policy; for one, he is adamant to institute changes in the US’ H1-B Visa programme to limit the number of foreign employees in the US’ technology industries.
Along the same line, Trump has also signed a bill repealing the US’ Internet Service Provider privacy rules, which currently impose limits on how ISPs can use and sell customer data. Defenders of civil liberties believe it is a blow to the people’s privacy rights. Further, Trump’s appointment of one of the fiercest critics of the open-internet norm, Ajit Pai, as head of the Federal Communications Commission (FCC) has challenged the principles of net neutrality which were laid out only two years ago under Tom Wheeler’s Open Internet Order.
Another stakeholder in the ongoing conversation on cyberspace is China. As American hegemony continues to wane, China is offering alternatives and is working relentlessly to ensure that it has a role in defining the future of cyberspace. Tomorrow’s digital trade and the flow of bits and bytes may well be very different from the model envisaged by the creators of the internet.
In the first half of 2017, China announced its ambitious blueprint to connect Asia through a series of rail, road, port and energy infrastructure projects. Even before that, it was already at an advanced stage of being a key player in the manufacture of global digital goods. According to McKinsey, China is the world’s largest e-commerce market, accounting for more than 40 percent of the value of e-commerce transactions worldwide. Mobile payments in China amount to approximately 50 times that of the US, fuelled by the widespread adoption of e-wallets across its cities. One in three of the world’s 262 unicorns are Chinese, making up 43 percent of the global value of these companies. In 2015, the Chinese government signed off on its “Made in China 2025” and “Internet Plus” initiatives that aim to digitise China’s economy by integrating artificial intelligence, robotics, and digital services into manufacturing processes.
As part of its efforts to take the lead in the digital arena, China is making it clear that the retreat of the Atlantic powers will be complemented by Chinese propositions on digital commons. A March 2015 white paper setting out the vision for the Belt and Road Initiative (BRI) called for growth in digital trade and the expansion of communications networks to develop “an information silk road.” State-owned Chinese telecommunication companies are increasingly investing in Asian countries to develop digital infrastructure; even private players like ZTE are investing in fiber optic cables in countries like Afghanistan.
In 2016, China released its first ever “National Cyberspace Security Strategy” to set out its positions on cyberspace development and security. Interestingly, the strategy sees cyber security as “the nation’s new territory for sovereignty.” At the 2016 World Internet Conference in Wuzhen, President Xi Jingping declared, “We should respect the right of individual countries to independently choose their own path of cyberspace development, model of cyberspace regulation and Internet public policies.”
In characterising the internet as a fundamental domain of state control, China is challenging the long-held assumptions and principles that have governed the internet and have allowed it to proliferate over the past few decades.
The US’ apparent withdrawal from international engagement in cyberspace and China’s economic and political advance may well rewrite the rules of digital trade and openness in ways not envisaged by the internet’s inventors. Neither of these two actors, however, will unilaterally script this new story, given that the effects of digital networks in economic and social activity are now widespread and diffused. From the very beginning, the evolution of technology has defied prediction and delineation. As it becomes more ingrained in human life, technology itself will rewrite traditional notions of ethics and social contract. This new ‘machine conscience’ will result in fresh challenges for policymakers and technologists alike.
The rapid pace of innovation in AI is heralding a world that is keen on moving from governing through data to being governed by data. While these developments will have transformational effects on the economy, they will also challenge the basis of human autonomy and ethics. Hillary Clinton’s reliance on algorithmic decision-making during the US presidential elections has already offered us a glimpse into the inherent weaknesses of this new paradigm. As algorithms pervade every aspect of people’s lives, they will determine most personal choices. However, it is worrying that these developments are taking place at a time when it is still unclear how machines will replicate the social values and norms that human beings instinctively understand. This fear has prompted a fierce debate over the regulation of autonomous weapons, which are designed to be capable of making life-and-death decisions. Today, speculation is rife on what the future will look like when people’s decisions are, as one commentator put it, “more mathematical than inspirational.”
A future that is scripted through code, and not norms, may be cause for concern. As Vidisha Mishra and Madhulika Srikumar caution in ‘Gender bias in artificial intelligence’, algorithms written by humans should not reflect human biases and inequities. Instead, technology should be developed to empower, engage and enlighten. In ‘Vulnerability, dependency, and profitability in a digital universe’, Urvashi Aneja writes that people’s ever-increasing dependency on technology seems “unwise”, given the vulnerability of information infrastructures.
As the incumbent powers grapple with the changing dynamics of technology, emerging economies are gearing up to leverage it for the next billion users. Regulators are tackling the challenge of improving connectivity to harness the transformative potential of the internet. In ‘The Importance of the open internet in driving internet adoption and growth’, Michael Khoo and Peter Lovelock argue that governments in Asia need to ensure favourable market conditions and foster an open-internet environment that is non-discriminatory, neutral, and accessible. Similarly, Amelia Andersdotter, in ‘Has the time come for less red-tape in Indian telecom?’, looks at the role of regulation in facilitating adoption. The piece describes the introduction (and eventual removal) of licence and registration requirements for public WiFi in Italy and the lessons that India might learn from that strategy.
In this respect, a parallel transformation that is equally significant is India’s digital payments explosion. Digital transactions in India have quadrupled in the past year, spurred in part by the demonetisation of 86 percent the country’s currency and, in part, from the impetus provided by the Aadhaar initiative. The Aadhaar platform that sought to increase access and assist in the provision of subsidies has mass-sourced efficiencies, cut down the cost of transacting online, and moved bigger populations into the mainstream, formal economy than any other policy in recent history.
The success in the adoption of the Aadhaar ecosystem can serve as a model for other emerging economies struggling with efficient delivery of services. Coupled with open application programming interface layers that allow private companies to utilise its biometric database in a secure manner, the Aadhaar ecosystem offers a unique model that has the potential to catalyse growth and innovation in digital economies around the world.
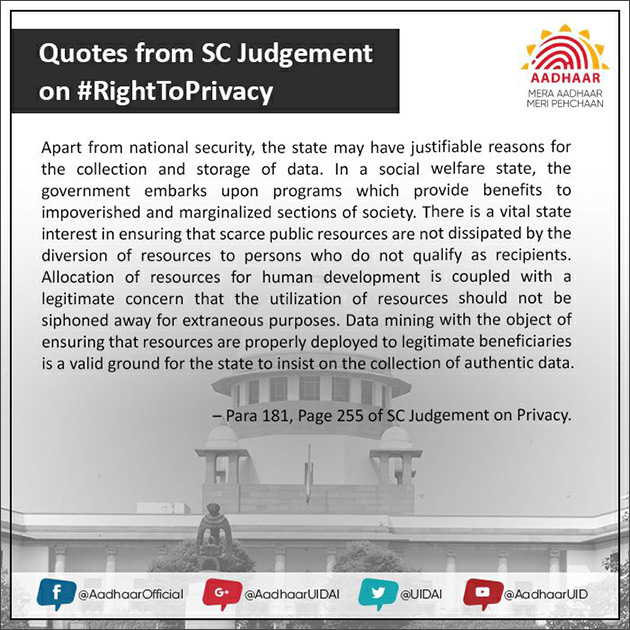
In turn, these developments have had the cascading effect of strengthening civil liberties and improving the security of cyberspace. In August this year, a nine-judge bench of the Indian Supreme Court unanimously ruled that privacy is a fundamental right under the Constitution, harmonising over 60 years of conflicting pronouncements and granting the strongest possible protections to people’s right to privacy. In fact, the Court has made specific references to informational privacy and the need to complement the right to privacy with strong data protection laws.
The Indian government, for its part, has established a 10-member expert committee to review existing data protection rules. These recommendations—likely to be tabled in the parliament later this year—can have the effect of modernising privacy protections and bringing them in line with international standards.
Governments in emerging economies should now go a step forward and make significant investments in newer technologies to give an additional spurt to their governance mechanism. Blockchain is one such technology. Originally seen as a financial innovation, blockchain’s potential is now being recognised in a wide array of industries such as land rights, defence, art, precious jewels, and music. This technology has the potential to address even more complex issues such as checking the proliferation of nuclear stockpiles. In ‘Licence in chains: Could media content be licensed through blockchains?’, Meghna Bal explores how this innovation could be used to facilitate a more transparent licensing scheme for artistic copyrights, allowing the industry to manage the challenges that come with large copyright societies.
In ‘Challenges for a new economy: the Fourth Industrial Revolution’, Logan Finucan describes how the so-called “Fourth Industrial Revolution” (4IR) will bring significant progress in productivity, such as in the use of advanced robotics and manufacturing techniques, the Internet of Things (IoT) and machine-to-machine (M2M) connections on a massive scale, autonomous vehicles, and new industrial materials, all powered by artificial intelligence (AI) and pervasive big data analytics. Meanwhile, in ‘Applications and policy considerations for AI in cyber security and public services’, Ryan Johnson and Seha Yatim ponder the question of how to manage the complex interrelationships between these new technologies, as well as the disruption they are likely to cause.
As economies increasingly rely on new technologies, it will be critical for them to ensure the stability of cyberspace and the integrity of their networks. This will require cross-sectoral cooperation – including that with the private sector – fostered by mutual trust. Three contributions in this volume ponder the issues related to the interaction between the private and public spheres in administering security over the internet. Chelsey Slack, in ‘Tempering national and international tensions in cyberspace’,provides an outline of the global discourse on security in cyberspace and highlights the need for cooperation among different actors. In ‘The hybridisation of cyber security governance’, Dennis Broeders identifies the emergence of cyber security assemblages – made up of government agencies, transnational corporations and cyber security companies. Finally, Nikolas Ott and Hugo Zylberberg argue in ‘Addressing international security challenges while avoiding internet fragmentation’ for interoperable policy regulations.
In addition to cyber stability, an equally important task for states would be to manage the “real-world” effects of new technologies, which spill into offline considerations of security and prosperity. Technology is in the process of rewriting the nature of the relationship between individuals, states and businesses. Machine learning and AI will question dominant models of labour, economics and social stability. However, these very technologies have the capacity to usher in unprecedented innovation, growth and progress. As the next billion internet users emerge from Asia and Africa, governments around the world should explore technological solutions to expand the scope and effectiveness of their governance. But as the presidential elections in the United States and the rise of China indicate, there is enough evidence to guard against any positive and deterministic outcomes from technology. It is likely that new innovations are going to be political and politicised: no longer can evangelists sitting in the comfort of their offices in Silicon Valley claim to be neutral vendors of technology, selling their products for the public good. As technological effects on offline realities become more prominent, state and non-state actors must be mindful of the effects of such rapid change on social structures. While technology can, and does, magnify existing faultlines between peoples and nations, it also offers a fleeting glimpse of greater harmony between humans, machines and states. The rules that will determine the nature of this relationship are still being written. The responsibility of all stakeholders is to ensure that new technologies do not lead to the creation of a world order that is haunted by the conflicts of the past, but rather of a new social contract that abandons the shackles of inequity and promises peace and progress.
To read the full issue, click here.